Office 365: How to restrict mailbox access of Azure applications in app-only mode
We already described how to register an application to access Exchange Online mailboxes via EWS or Microsoft Graph API in app-only mode, suitable for unattended application.
However, default settings allow applications to access all mailboxes in the organization, which might be undesirable in many scenarios. This guide below describes what needs to be done to restrict access of those applications to a single mailbox using the New-ApplicationAccessPolicy cmdlet.
Get your application ID
First, you have to determine the
AppIdof your application. In Azure Portal ⇒ expand the left menu ⇒ selectAzure Active Directory⇒ selectApp registrations⇒ locate your desired application.(Azure Portal is constantly evolving, so if you cannot find this page, use the search bar and locate
App registrations.)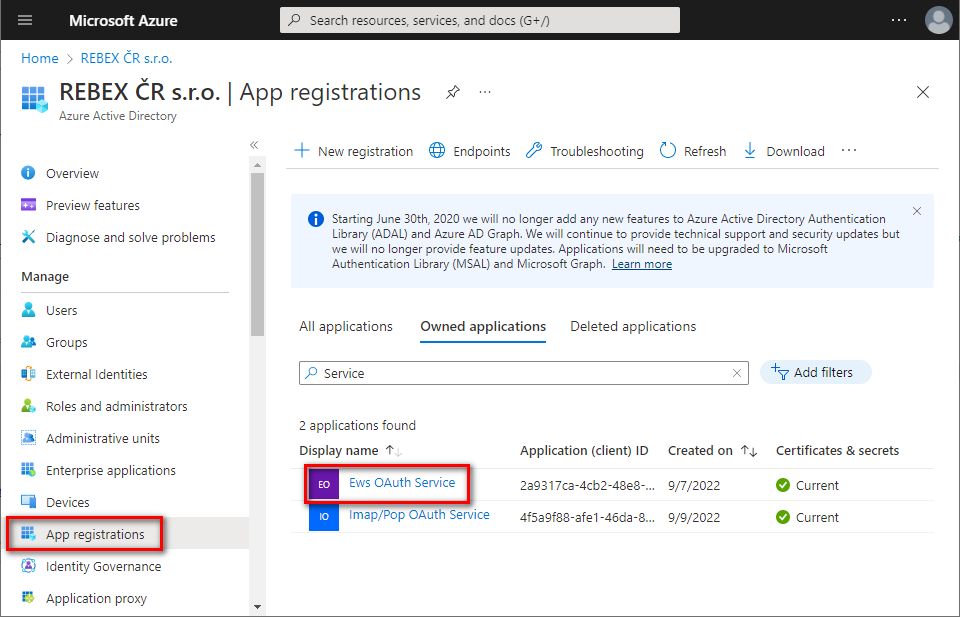
On the
Overviewpage, you can find theAppIdlisted asApplication (client) ID: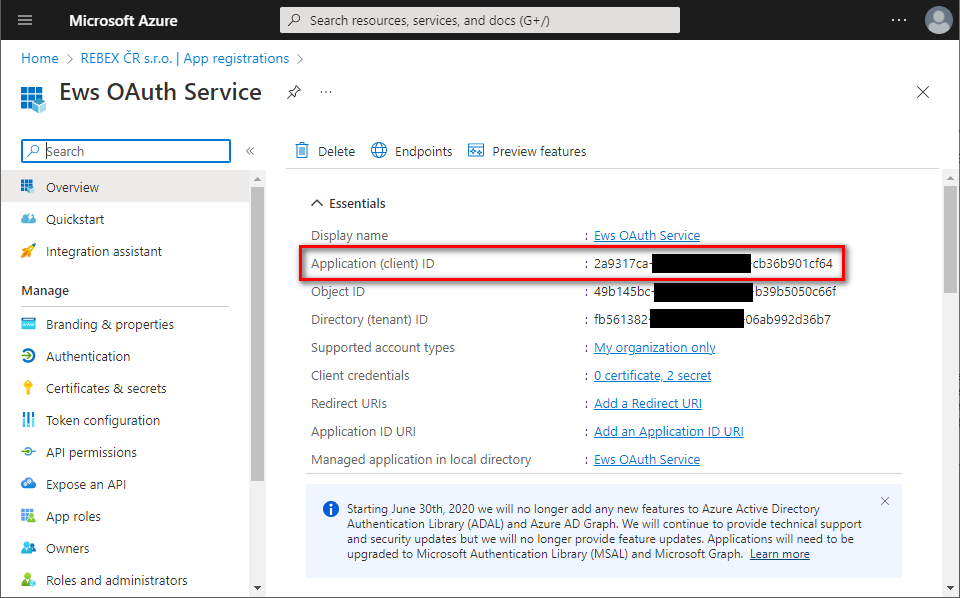
Restrict access to a single mailbox
Install the
ExchangeOnlineManagementPowerShell module that contains theNew-ApplicationAccessPolicycmdlet. (You can skip this step if you have already installed this PowerShell module.)Open your PowerShell as Administrator, and run:
Install-Module -Name ExchangeOnlineManagementConfirm installation from
PSGalleryby typingY+Enter.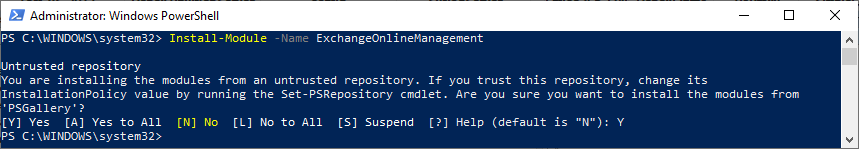
(Wondering why the module installs from an untrusted repository? See this Azure-PowerShell issue.)
Restrict application's access to a single mailbox. Please note that you will be asked to log into your Azure account.
$AppId = "YOUR_APP_ID_HERE" $Description = "Some description here" $Mailbox = "someone@example.org" Connect-ExchangeOnline New-ApplicationAccessPolicy -AccessRight RestrictAccess -AppId $AppId -PolicyScopeGroupId $Mailbox -Description $Description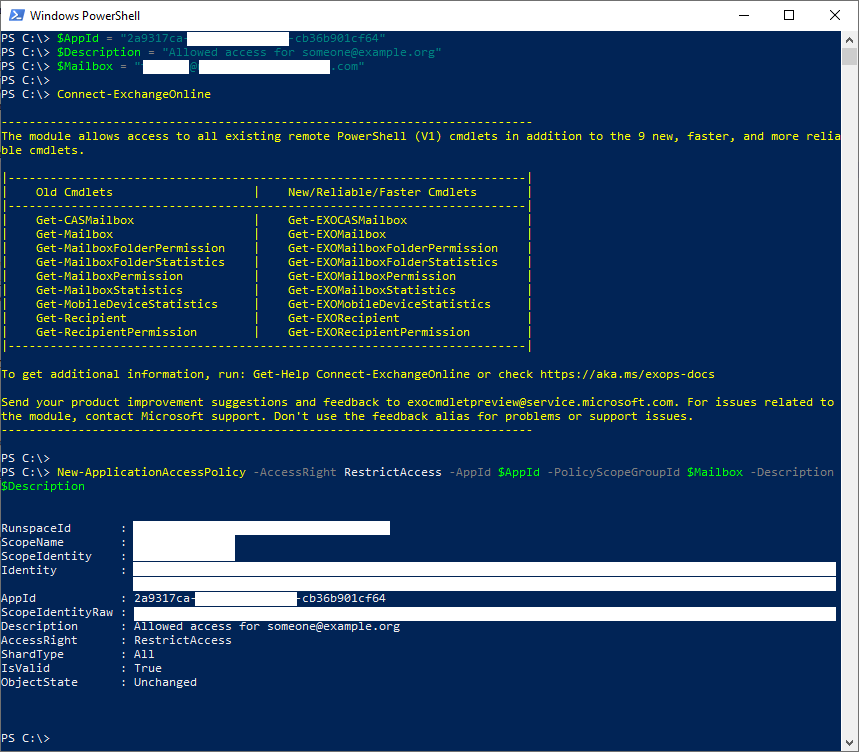
Congratulations! As soon as the changes take effect (which can reportedly take up to an hour), your application will only have access to the specified
$Mailbox. If you want to grant access to another mailbox, just run the script again with different$Mailboxand$Description. This way, you can explicitly grant access to all mailboxes you need.
Any issues?
Need help or have a question? Ask at Rebex Q&A Forum.