Rebex Buru SFTP Server 2.8.0: SSH public key management overhaul
We have released Rebex Buru SFTP Server v2.8.0. Here is an overview of changes, fixes and improvements.
New CLI commands for SSH public key management
burusftp user key add -u guybrush -f ed25519.pub -c "definitely guybrush's key"
burusftp user key delete -u guybrush -t ed25519 # oops
While using Buru SFTP Server internally, we found that user update command is quite cumbersome when dealing with public keys.
So we decided to create new lightweight commands to manage the keys - enter user key add and user key delete.
Using these commands you can manage users' public keys efficiently, for example remove specific compromised keys across all users.
Web Administration SSH public key management improvements
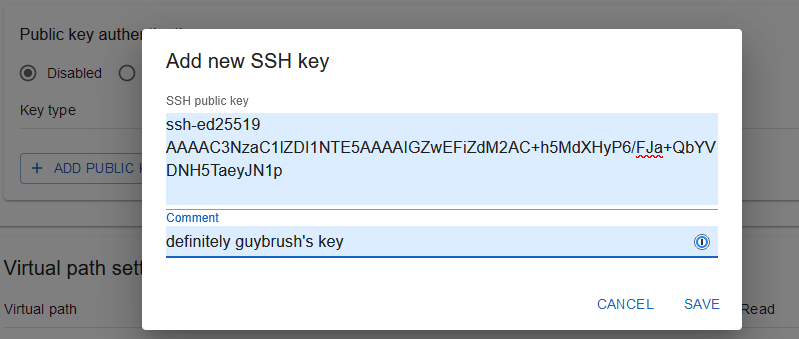
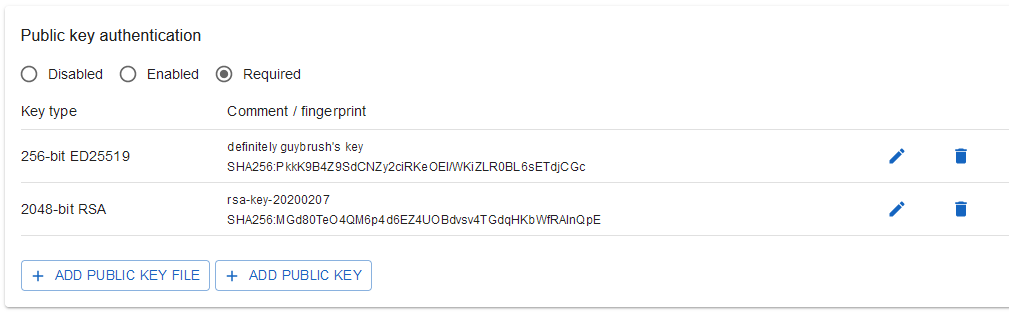
Prior to version 2.8.0 administrators could only upload public key files. It is now possible to also enter keys directly in the Web Administration. This is especially handy if you keep your keys off the filesystem, for example in a password manager such as 1Password.
Related to the previously mentioned features, you can now assign comments to users' SSH public keys.
This can be done when importing new keys (also using CLI user key add) or for already registered keys.
SFTP encoding changed to UTF-8
Switching from win-1252 to UTF-8 allows transferring files with non-latin characters without mangling their file names. We believe this change will not cause any issues for our users as encoding of latin characters remains the same but we consider it a breaking change nevertheless.
Safer behavior when removing SSH public keys from users
Prior to version 2.8.0, removing the last SSH key from a user using user update <username> --remove-keys <key> automatically disabled public key authentication.
With multi-factor authentication this effectively downgraded the credentials needed to password only, which might or might not be what the user wanted.
To avoid any confusion, we now keep the original value for public key authentication (enabled, required or disabled), no matter whether or not user has any public keys left.
This in effect also means that when the last key is removed and public key authentication is still set to required, then the user will not be able to log in.
To allow the user to log in, either disable public key authentication (user update <username> --key-auth disabled) or add a new key to the user using (user key add).
# prior version 2.8.0
# sets multi-factor authentication
burusftp user add guybrush --keys ed25519.pub --password "elaine"
# removes key and disables public key authentication
burusftp user update lechuck --remove-keys ed25519
# user can now login with password only
# version 2.8.0+
burusftp user add guybrush --keys ed25519.pub --password "elaine"
# only removes key
burusftp user update lechuck --remove-keys ed25519
# user cannot login as multifactor authentication is still active but user has no assigned keys
burusftp user update lechuck --key-auth disabled
# user can now login with password only
Issues and feature requests on Github
You can report issues and submit feature requests on our Github issue tracker. For discussions and specific problems please keep using our support forum.
Minor fixes and improvements
- 2.8.0
- Buru SFTP Command Line shortcut now opens shell in the installation directory (previously in Windows SYSTEM directory).
- CLI -
user update --remove-keysnow acceptsdsa;ecdsanow matches any ECDSA key.
- CLI - user public keys can now be specified directly using
user add --keys <key>,user update --add-keys <key>anduser update --set-keys <key>. - CLI - virtual paths in path and path delete commands can now be specified without
/prefix. - CLI - when virtual path (
-v <path>) inpathandpath deletecommands is not specified, it defaults to root (/) path.
- 2.7.3
- Web Admin - fixed performance issue on user edit page.
For complete list of fixes and improvements see Release notes